|
to effectively parent your children! I have said this before, and I say this often; You do not need to know more about technology than your child, period. However, you do need to control the stream of information available to your child. In an effort to help you with this I have posted some information about sites gaining in popularity I had the opportunity to meet with several parents this summer who all have the same basic concern. "How do I parent my child in this technological era?" The basic premise is that because our children are such avid users of technology then we as parents are left behind, hoping that our kids stay safe. Years ago it was just concern over computer . Internet enabled devices are no different. Do you really know what your child is up to online? If not, maybe investing in some monitoring software like Besecure would help, or collect all devices at night. There has been a recent surge in sites or games that are seemingly harmless but can later put your child at risk for inappropriate contact or bullying. Social Meeps, Roblox and Minecraft are all sites that are fun and are seemingly innocent. I believe that they have been created with the best of intentions. Furthermore, a couple of them are highly educational. However, they these sites do allow for the very young to interact with unknown others, that is where we as parents lose some control. Social Meeps is a fun site that basically is one big virtual chat area. The "meeps" (avatars) are highly customizable, customization is where Social Meeps makes money. One can pay to upgrade his/her meep with a variety of skins and accessories. This site drew my attention when I was working with a couple eleven year-olds who were talking about it. Social Meeps does have a Terms of Service that must be accepted that states:"Most content on the message boards come straight from other Social Meeps users, not from administrative staff. If you see anything mean or nasty on the site, or anyone sends you anything that makes you uncomfortable or asks for your password or personal information (such as your name, address or phone number), please let us know immediately by using the 'Report Abuse' button next to any user-generated content, so that we can handle it right away!" What Social Meeps and many other social sites neglect to state is that the most dangerous users do not outright ask for personal information when scoping out a victim. The process of grooming can go for months to years. One of my students said it best, “My parents don’t know anything about technology, but I know what they expect from me”. Such a classic statement, and I was so proud of her. Be involved, be nosey. You’re a parent, it is our God-given right to be in our kid’s business. It is better to be overly cautious, then regret not being cautious enough.
Look out for my next posts on Roblox and Minecraft.
0 Comments
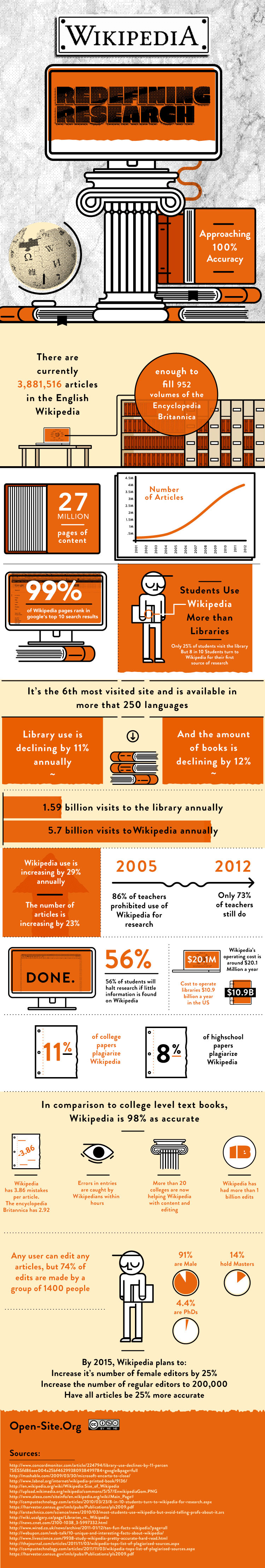
This past March, Encyclopedia Britannica announced that the printed volumes of the encyclopedia are a thing of the past and all focus will be dedicated electronic delivery and educational programs. The demise of the once status-symbol leather bound book was triggered by the rise of social knowledge. Or, in other-words, sites like Wikipedia. Thank you to Jennifer Rhee who forwarded me her info-graphic on how Wikipedia is changing the face of research. There are several thoughts that arise while studying Jen's graphic. I recently consulted on a research project for 10th graders, and standard policy for research projects is that only databases are allowed. Wikipedia and Google were absolutely shunned. I couldn't help but wonder "why?". Google Scholar is a fantastic resource, and Wikipedia, for being a social construct, is a great place to begin research. Of course I believe that it is very important for all students to have a command of databases and develop strong skills in information literacy. (1. “...the ability to know when there is a need for information, to be able to identify, locate, evaluate, and effectively use that information for the issue or problem at hand.”) Information Literacy is one of the most necessary skills needed to be successful in the 21st Century. However, I see the same perpetuating limitations imposed on students time and again. I believe restricting the resources available to students is also limiting their creativity. David Warlick, a well known educational technology speaker, asked at the Tech Expo (Hosted by the Lower Hudson Regional Information Center) "What if we said 'Surprise me' to our students?" At first blush I was intimidated by this question, but its truth is unavoidable, what do we have to fear? That students will have inaccurate information? That students will plagiarize? The students that make those poor choices would likely do the same regardless of the resources they use. The key is not in the resources, but teaching students information literacy skills. It makes no difference to me what tools my students want to use. My students are going to utilize the tools that are most intuitive for them, students tend to be on cutting edge using new resources. Of course I want my students to be adept at using databases and equally versed on the Google Research Tool, and Google Scholar. But most importantly I need them to understand how to find and evaluate resources that are pertinent for them. Have you asked your children how they research? Or, how they evaluate their resources? It is a worthwhile conversation to have. 1.http://en.wikipedia.org/wiki/Information_literacy
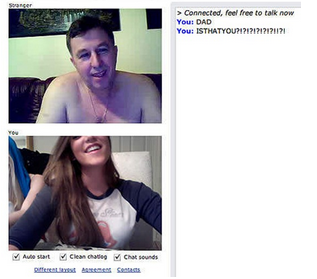
Dear Jennifer: I am writing to you as a mom for advice. I just found out some friends of my daughter are going onto chatroulette and omegle. I was not familiar with these sites so I spent a little time looking around. It is clear that this is not a place for middle school kids to be, even if they only use the TEXT option. I want to appeal to my daughter on reasons not to use these sites and was hoping you could offer some ideas on links or stories that I could use as examples. I know this issue is important to you so that is why I am asking for your assistance. Thanks, Debbie B Dear Debbie: Thank you for the question. For anyone who is unfamiliar with these sites, Chatroullette and Omegele are websites that enable people to video chat with a complete stranger. Chatroulette and Omegele are just two of the more popular random video chatting sites. There are very serious concerns about the use of these sites with children and teens. Chatroulette was created by Andrey Ternovskiy, a 17-year-old high school student in Moscow. He told the New York Times he initially created the site for "fun" and to “connect randomly with global users.” When Andrey created Chatroulette, I doubt that he had the foresight to see that there would be a multitude of adults who are in various stages of undress being paired with children. But that is what’s happening. Unfortunately, there are many kids and tweens that are regularly logging on to Chatroulette and being exposed to content that is inappropriate and possibly dangerous. It is common for teens and tweens to get together for Chatroulette parties, but it is also getting more common for young kids who are left on their own to log on and interact with strangers. One example is an eight year old boy who is notorious on Chatroulette for being vulgar and asking girls to flash him. Here is a summary of the dangers of these sites: 1. Your child can be exposed to adults who are nude and looking for a witness for their actions. 2. If your child is convinced to expose herself, it is very likely that it is being recorded. This can later be posted on the internet and identified by your child's friends, teachers or co-workers. There are actually a few posts on the Web titled "How to ruin someone's life" using Chatroulette. 3. Many people on Chatroulette do not care about the feelings of the person on the other end of the chat. Your child may be subjected to insults and slurs. A user can flag another's posts, but that rarely happens. Therefore, your child may come away from a Chatroulette session self- conscious and vulnerable. In summary, this is absolutely no place for children. However, like I have stated many times, risky behavior does not come from just “bad” kids, but from kids. When helping parents that are concerned about Chatroulette, I must ask the following questions: 1. Does your child have an Internet capable computer in her room? If so, disable the network card or take the computer out. You would most likely not allow your child to go to a party with no adult supervision. The Internet is no different. The biggest parental mistake that I see is that they allow their child to have unrestricted and unsupervised access to the Internet from the privacy of a bedroom. 2. Do you have content filters set up? Nearly all computers, hand-held devices and their browsers have the ability to block content and sites. If you are unsure how to do this, just Google the browser name and parent controls. For example, use the search terms “Parent controls safari” and “blocking websites internet explorer” and you will no doubt find sites that walk you through these procedures step by step. 3. Do you have monitoring software installed on your computer and all hand-held devices? If not, do so, and fast. You will never regret being an overly cautious parent. But you can regret not being cautious enough. Software I have recommended on my blog, http://www.bsecure.com/, monitors all devices and computers. It can automatically shut off a device at a desired time and email the parent of all places visited on the browser, as well as show texts and pictures sent or received on the computer and hand-held devices. I hope this post is useful to parents. Please keep the questions coming. I am here to help. A crucial point I hope to pass on in my blog is that all teens (and adults at times) will make impulsive decisions that can impact the rest of their lives. Digital media and the Internet further compound this problem by indelibly branding mistakes on the Internet, which can later compromise reputations, college admissions, job possibilities and drive some to suicide.
There are endless stories available on the Web where a Facebook post, tweet or picture has caused the demise of jobs, friendships or even lives. All of this usually occurs without the teen’s parents being aware of any issues. The same can be said for the parents of teens that are purely victims of bad online behavior. Jessie Logan was an eighteen year old girl with a bright future. She committed suicide after a sexted picture of her made its way through her high school and then college. Her mother found out about the picture after it began circulating, and because Jesse was eighteen and not a minor, there was little that could be done legally. Ryan Halligan was a thirteen year old boy who, unbeknownst to his parents, was being severely bullied online and in person. Ryan was set up to be mocked online by a girl he liked, and as a result, killed himself. Megan Meier and Phoebe Prince are also victims of what has been dubbed “bullycide”. The common thread in all of these instances is the parents were unaware of their child’s online activities. There are many tools available to parents today that can aid in what I call “digital parenting.” These tools help parents stay one step ahead of their children, in spite of their children’s best efforts to hide their activities. For example, 32 percent of teens clear the browser history to hide what they do online from their parents. (Harris Interactive-McAfee, 2008) What can you do? Invest in monitoring software: www.Bsecure.com There is now software available that will allow parents to see all of their children’s activity online and on their phone. One piece of software that I would like to recommend to my readers is Bsecure Online (6.1). Bsecure has been highly reviewed by industry media# and I believe it is the most comprehensive service for concerned parents. Bsecure will monitor all computers (PC and Mac) , phones and other mobile devices. Bsecure notifies parents of your their child’s social media interactions, content of downloads, sets time limits for mobile devices (automatic shut off at bedtime), and filters content on home and mobile browsers. This is truly one-stop shopping for the digital parent. There is far more than I am mentioning in this post. As always, please do not hesitate to contact me with questions. I had the opportunity to present today at the Hudson Valley NYSCATE Conference. It was exciting to present all my endeavors in the realm of cyber safety. Reflecting on my presentation I think next time I am going to separate the student/parent approach and focus on one theme. Additional information and resources used for my presentation can be found here.
I am also planning for some community classes, so please stay tuned! Cyber-predators are a topic I loathe discussing. The research I have done on predators has made me lose sleep and eventually, when researching, I stumble across cases I wish I could forget. But the research is worth it, helping parents and kids understand how predators work, and how to spot red flags is one of the primary reasons this blog started.
What is a Cyber Predator? Technically speaking, a cyber-predator is someone who uses digital media to establish and manipulate a relationship with his victim. Most commonly, this is sexual in nature, but can also involve manipulation for money or other things. Lately, some predators just have victims send compromising pictures and videos. The Process of Grooming- Cyber Predators are well versed in establishing a relationship with their victims and have no qualms about taking months to "groom" their victims. Grooming- is the process by which a predator slowly gets his victim to drop his/her guard. This is done by first appearing like the one who "understands" the victim. Many teens feel that no one understands them, a predator turns this his advantage. Predators become the victim's best friend and the relationship becomes nearly addictive. Predators will slowly begin to exploit a child's natural curiosity about sex and begin to introduce topics and media that is sexual in nature. From my research I have found predators exploit victims in two distinct ways: Direct abuse- Where the predator grooms the victim and convinces him/her to meet in a public or private place. Indirect abuse-Where the predator grooms the victim and convinces them to send revealing pictures and videos of themselves. Neither of these two types of abuse are exclusive, for example. A common tactic for a predator has been to convince a victim to send nude pictures and video of themselves. Later, the predator uses this leverage to force a meeting with the victim and blackmail them into sexual acts. One such predator is Nicolas Stone, who convinced 55 girls between the ages of 12-17 to get undressed in front of their webcam. These pictures and videos were later used to create pornographic material and was published to the Web. Nicolas also convinced a number of the girls to meet him in person and engage in sex acts. At the time of sentencing Nicolas was 35 years old, he has three children. What can you do? 1. Get protective software that logs every key-stroke, conversation and media that is exchanged on your computer. God forbid your child is disappears, this software could help you locate them. There is similar software available for cell-phones as well. 2. Keep all web-enabled devices OUT of the teens rooms and in a public area of the house. You can disable a laptop wifi card so the laptop needs a cable to access the internet. At bedtime, collect phones. 3. Watch all deliveries, or have the post office hold them for you. Predators will send pre-paid cell phones, plane tickets and bus tickets. Predators prefer having a victim to come to them, then they have not taken a minor across state lines. 4. Have your child's password for every social media account they have. If you are not sure what accounts they have- check the history on your Internet Browser and see where your child goes online. "Friending" your child does not work! 5. Check http://www.familywatchdog.us/ to stay apprised of any predators in your immediate area. However, most predators do travel quite a bit to meet victims Creating a Google Alert One fantastic tool for your digital parenting arsenal is the "Google Alert." The Google Alert was originally created for consumers to monitor the Web for new content on a specific topic. To create an alert, first decide on the search criteria, then enter a few more parameters about the search results. Once complete, the alert will notify the user if new information appears on the Web fitting the search criteria. What does this mean for parents? Well, parents can create an automatic search engine that will notify them when any type of media is tagged with their child’s name. In the age of digital parenting, this type of tool is a must. And better yet, it is free. Here is how you do it:
1. Go to www.google.com/alerts 2. Enter your child’s name in the first search field. Use quotes to make sure the name is searched as a complete phrase and not separate words. 3. In the "Result type" field, select "Everything." 4. In the "How often" field, select the frequency by which you would like to receive notifications. 5. In the "How many" field, select "Only the best results" 6. In the "Deliver to" field, type in the email address to which the notifications will be sent. 7. If your child has a commonly used nickname, you may want to create an alert for that name as well. If you need any further assistance or have questions, please email me jenn.cronk@gmail.com or visit my Website www.transparentlyteaching.com.  Recently E-School News published the article Teen ‘sexting’: Less Common than Parents, Educators Might Fear. The article discusses the current statistics about 'Sexting' (the electronic transmission of nude or semi nude pictures usually via cellphone). Essentially the article states that Sexting is not as serious as teachers and parents think. The study is based on a survey of 1,560 children, 10 to 17 years old, who use the internet. I challenge the validity of these findings based on the age range involved. As of right now, the study states that slightly more than 7 percent of children participating in this study have received, sent or taken inappropriate pictures of themselves or others. I speculate if the focus of the group was reduced to only include high school age students this percentage would sharply increase. Upon reading the article I did my own research ( aka: asking my students) about their knowledge about kids that participate in Sexting. My results revealed about 70% of my students in one class know of sexted images circulating. In previous years I have gone so far to conduct my own surveys and collect data. Once High School begins, the Sexting numbers rise. I do agree, with one assertion of the study; that promiscuous teens are more likely to engage in Sexting than more conservative teens. I suggest that we all keep in mind that even teens who are rational and not promiscuous can be pressured into sexting. What parents need to know: How does Sexting effect teens? A 'Sext' is most often used as relationship currency between boys and girls. It is usually a girl who is seeking to win the affection of a boy or to keep the interest of a boyfriend. As with the case of Jessie Logan, she sent a Sext of herself to a boyfriend. Upon breaking up, the boy spread the picture of Jessie around her High School. Jessie was taunted mercilessly because of the picture, but she persevered through High School and graduated. Sadly, when Jessie made it to college, she found the sext had circulated there as well and she took her life. The Legal Issue: Beyond the horrible repercussions that people like Jessie suffer, there are legal ramifications to Sexting as well. First, anytime a teen under the age of 18 takes a nude or partially nude picture of them selves- in the eyes of the law that teen is now in the possession of child pornography. If that teen 'sexts' that picture to anyone else, he or she has now trafficked child pornography. For example, child pornography charges were brought against six teenagers in Pennsylvania in January 2009 after three girls sent sexually explicit photographs to three male classmates. A More troubling fact is that teens who are charged with possession and trafficking child pornography from Sexting, will most likely be labeled a sex offender for the rest of their lives. So, perhaps the study mentioned by E-School News is correct and Sexting is not as pervasive as once thought. Regardless, Sexting is a very real issue that already has robbed teens of their reputation and lives. I strongly suggest that all parents sit down with their teens and discuss Sexting and its ramifications. I had done a post earlier in the year entitled Yes Parents, I do use cellphones in my English classes for my students. Today, this post is for my colleagues at our December faculty meeting. The video below is a great introduction to Poll Everywhere Today I gave a brief summary of my favorite mobile tools for the classroom at our faculty meeting. This post will helpfully support my fellow teachers in their effort to use mobile technology in the classroom. Poll Everywhere and Remind101 are staples for my classes. Remind101 created by Brett Kopf and his brother, is designed to send text blasts from teacher to student while protecting the privacy of both.
I will upload the hand-outs shortly so please check back. Over the past couple of days, there has been much chatter from ed tech bloggers about the newest Norton report about cyber baiting. Cyber baiting is when students instigate or taunt their teachers, capture the teacher "losing it" with the class, (usually on a smartphone) and post the teacher's outburst to the Web. Countries where this becoming more prevalent are the United States, United Kingdom, Australia and New Zealand. Furthermore, according to the Norton Online Family Report, one in five teachers reported to have experienced or have known a colleague who has experienced cyber baiting. Doing my own extensive research (aka asking my own students) I found many, many disturbing videos. In some cases, students are clearly setting the teacher up for a fall. Others, I believe, are teachers who I believe are totally overwhelmed or who have no business teaching. The above teacher is clearly trying to teach and is obviously frustrated. In the comment section of the above video, students are actually speaking out against the trouble-makers. As a fellow teacher, I can sympathize with this teacher's frustrations. I feel bad for the teacher because he is unaware that he is being recorded and because he obviously has some chatter going on while he is trying to give directions. One suggestion I have for any teacher in this situation is to read the book The First Days of School, by Harry Wong. There are amazing techniques offered for removing undesirable behavior that is a personal attack against the teacher. As a teacher, if I can keep the behavior separate from the child, and not allow it to affect me personally, then half the battle is won. Harry Wong is a great resource for any teacher looking to hone his/her management skills. Now this video on the other hand, is over the top. The teacher is obviously upset that the student has destroyed a calculator. But there are several things wrong with this display of frustration. Acting this way does no good for either party. Was he cyber baited into acting this way? I am unsure, but nevertheless it was caught by camera phone and uploaded to YouTube. Now his bad day will always be available for any future students or parents to see. Yes, he could jump through a few hoops and have the content removed from YouTube and pulled from a Google search. I think this is a lesson for all teachers; we no longer have to worry only about what we publish online, but what may be published about us as well.
What to do? 1. Make sure your school and your colleagues are aware that cyber baiting is a growing trend among teens. 2. Instruct colleagues to create a "Google Alert" whenever new content tagged with their name is published to the Web. 3. Find out if your school has any rules against recording devices in the class. 4. Remember, a teacher who loses it is lost. Bad behavior is not a personal attack usually. Have procedures and consequences in place and consistently follow them. Let's just hope technology does not advance to allow students to read our minds! :) |
Jennifer CronkI am a technology leader, professional developer, teacher, parent and proud owner of an IEP. Let's talk about some fabulous learning experiences. Archives
November 2019
Topics
All
|
Transparently Teaching




 RSS Feed
RSS Feed
